The secure online transactions in today’s digital economy matter greatly if you have a business or personal needs. Pasonet leads payment security and uses advanced encryption techniques to protect all transactions through its gateway. Their secure online payment system makes sending and receiving money simple while keeping sensitive information safe from threats.
Most payment platforms choose speed over security, but Pasonet technologies strikes the right balance. Users get quick payment processing without sacrificing protection. The system’s user-friendly interfaces make this strong security available to everyone – from single users to large corporations. Pasonet technologies private limited has built a platform that automates and simplifies tasks like networking, data processing, and monitoring. State-of-the-art encryption protocols protect all data continuously. The combination of security and efficiency on pas-net.com brings a major step forward in online payment solutions for businesses and personal use.
Security Architecture of Pasonet Technologies Private Limited
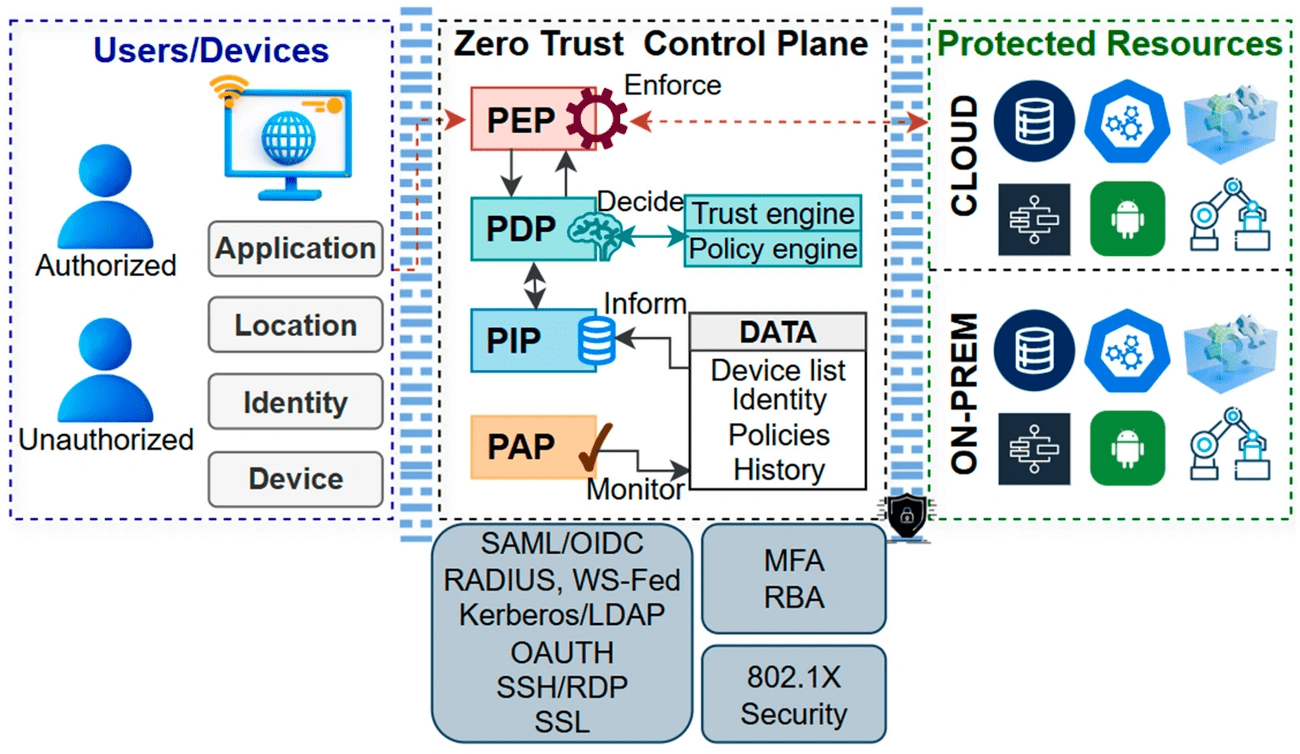
Image Source: MDPI
Pasonet Technologies Private Limited builds its edge in the market with a resilient security foundation ready for today’s cyber threats. The company makes big investments in network security infrastructure and sets up multiple protective barriers between potential attackers and sensitive user data.
Layered Security Model in Pasonet Infrastructure
Pasonet uses an integrated defense-in-depth strategy with its layered security model. A single security measure can’t protect against sophisticated threats. Multiple defensive layers work together to create barriers that attackers must overcome.
Physical security measures protect Pasonet’s data centers and hardware. Strict access controls guard server rooms while surveillance systems watch the physical infrastructure. Network security serves as the core of Pasonet’s defense strategy. Advanced firewalls and intrusion detection systems monitor and control all traffic going in and out.
Application-level security makes sure all software goes through strict security testing with regular updates to fix vulnerabilities. Data security—maybe the most critical layer—uses encryption for information stored and moving through the system. This keeps sensitive transaction data safe even if other defenses fail.
Pasonet knows people play a key role in security. The company runs complete staff training programs that turn employees into an extra security layer instead of weak points.
Zero Trust Network Access (ZTNA) Implementation
Pasonet’s security architecture centers on its Zero Trust Network Access implementation, which follows the rule “never trust, always verify.” Traditional security models trust internal network traffic, but Pasonet’s ZTNA treats every access request as a potential threat, whatever its source.
This radical alteration helps pas-net.com users in two ways. Access gets granted on a strict need-to-know basis, which cuts down the attack surface. Remote workers and third-party vendors can access Pasonet systems safely without weakening security standards.
The ZTNA system checks every user, device, and application before letting them access specific resources. These checks happen throughout each session, not just when users log in. If the system spots suspicious behavior during a session, it can cut off access right away.
Pasonet Technologies Private Limited does this through:
- Identity-based authentication that goes beyond IP-based access control
- Trust checks that watch for changes in device status and user behavior
- Deep inspection of all traffic, even for allowed connections
- Precise access control at the application level, separate from network setup
Cloud-Based Redundancy and Failover Systems
The third pillar of Pasonet’s security architecture uses strong redundancy measures to keep services running. Cloud-based redundancy spans multiple geographic regions. This creates an infrastructure that keeps working even during local disruptions.
Data redundancy means multiple copies of files exist across different locations and cloud storage providers. When one data center goes down, others take over naturally. This keeps transactions moving without interruption.
Network redundancy plays a big role too. Redundant connections, routers, and switches prevent service problems when network parts fail. Application redundancy spreads workloads across multiple instances to maintain availability during partial system failures.
Automatic failover systems redirect workloads or traffic to backup resources when they detect failures. Continuous monitoring and automated responses trigger failover processes or add resources as needed. This setup keeps pas-net.com running and secure in almost any situation.
Encryption Standards Used in Pasonet Transactions
Pasonet’s transaction security framework relies on encryption to protect sensitive financial information throughout its lifecycle. The company uses top-tier encryption standards that go beyond common security requirements. This creates a reliable shield that keeps user data safe from unauthorized access.
AES-256 Encryption for Data at Rest
Pasonet Technologies uses Advanced Encryption Standard (AES) with 256-bit keys to protect all stored data. This powerful symmetric encryption algorithm turns plain text into unreadable code through multiple rounds of mathematical processes. AES-256 uses a 128-bit block size where data splits into a 4×4 array containing 16 bytes, with each byte containing 8 bits.
AES-256’s security comes from its extensive transformation process. The algorithm runs 14 rounds of key expansion for Pasonet’s stored data, unlike AES-128’s 10 rounds. This extra complexity makes it much harder to crack through brute force attacks and cryptanalysis attempts.
AES-256 encryption on pas-net.com brings several key benefits:
- Impenetrable security – A 256-bit key length would need billions of years to break with today’s technology
- Government-grade protection – The U.S. government uses this same standard for classified information
- Increased data integrity – Payment information stays tamper-proof even if someone compromises storage devices
Pasonet makes sure this high-level encryption doesn’t slow down the system. They use specialized hardware acceleration to keep transactions quick while protecting all stored financial data.
TLS 1.3 for Data in Transit
Pasonet Technologies uses Transport Layer Security (TLS) 1.3—the latest and most secure version—to protect information moving across networks. This new version brings major improvements over older ones. Its redesigned key derivation functions let cryptographers analyze it better thanks to improved key separation properties.
TLS creates a secure channel between communicating parties that provides authentication, confidentiality, and integrity. When you connect to pas-net.com, TLS 1.3 starts a handshake where the server proves its identity with a digital certificate. Then both sides exchange cryptographic keys safely.
Pasonet’s TLS 1.3 implementation improves security in several ways:
The system only supports Authenticated Encryption with Associated Data (AEAD) algorithms, removing outdated ones. All handshake messages after ServerHello stay encrypted, which protects various extensions. The handshake state machine has a better structure that removes unnecessary messages.
This means Pasonet users’ sensitive information—personal and financial data—stays secure whether they use web browsers or mobile apps.
Key Rotation and Management Policies
Good key management matters as much as strong algorithms. Pasonet Technologies follows detailed key rotation policies. New encryption keys generate automatically every 90 days, in line with PCI DSS industry standards.
The system creates new key versions at set times. Different types of keys follow separate rotation schedules. Financial transaction encryption keys update at least every two years, meeting cryptographic best practices.
Pasonet’s key management system keeps track of versioned key URIs with encrypted data. This helps match the right key material to each encryption operation. Users can always decrypt their data without service interruptions.
The company also gets alerts through Event Grid integration before keys expire. This proactive approach helps prevent service disruptions while keeping security standards high.
These reliable encryption standards and smart key management practices help Pasonet create a secure space for financial transactions. Your sensitive information stays protected at every step of the payment process.
Authentication and Access Control Mechanisms
Pasonet’s security framework relies on robust authentication mechanisms that act as gatekeepers for all user interactions. Pasonet Technologies Private Limited uses layered access controls to ensure only authorized users can access sensitive financial information without compromising user experience.
OAuth 2.0 Integration for Third-Party Apps
Pasonet uses OAuth 2.0 authentication protocol to let third-party applications access data securely without exposing user credentials. This protocol adds the user role (resource owner) to the traditional client-server authentication model and requires explicit permission before accessing resources. Third-party applications receive tokens that represent specific access privileges instead of actual login credentials.
OAuth 2.0 gives pas-net.com users several benefits:
- Protection against credential sharing with third parties
- Granular control over what information third-party applications can access
- Knowing how to revoke access without changing passwords
The system supports both authorization code flow and client credentials flow. Users connecting external applications to their Pasonet accounts get redirected to Pasonet’s authentication server where they provide consent. The application then receives a temporary code that can be exchanged for an access token, which expires regularly to boost security.
Multi-Factor Authentication via SMS and Email
Pasonet Technologies strengthens account security beyond passwords through multi-factor authentication (MFA). Users must verify their identity through additional methods. This security measure reduces unauthorized access risks by a lot because it requires multiple verification factors.
Pasonet’s MFA system works through two main channels:
SMS Authentication: Users receive a one-time passcode (OTP) via text message to their registered mobile number after entering login credentials. They must enter this time-sensitive code to complete the login process. This ensures attackers cannot access accounts without the user’s phone, even if passwords are compromised.
Email Verification: Pasonet sends verification codes to the user’s registered email address for certain actions. These single-use codes add an extra authentication layer that proves especially useful for high-value transactions.
Research shows MFA can stop phishing attacks by requiring extra verification steps beyond password entry. This makes it vital for financial transactions. Users managing substantial financial assets through Pasonet get significant protection against cybercrime.
Session Timeout and Auto-Logout Features
Pas-net.com protects users from unauthorized access during inactive periods through automatic session termination. The system logs out users automatically after they stop interacting for a set time. This prevents unauthorized access to unattended accounts.
Pasonet follows financial industry standards with a five-minute inactivity timeout. The system shows a countdown prompt when users remain inactive for this duration. Users can extend their session if they’re still present. They must log in again to regain access after timeout occurs.
This timeout system provides two key security benefits:
- Protection against unauthorized access if users leave devices unattended
- Compliance with financial regulatory requirements, including PSD2 regulations for payment service providers
Pasonet also sets absolute session durations regardless of activity levels. Users must log in again periodically even during active sessions. This limits potential session hijacking attempts. The system immediately ends sessions when passwords change or suspicious activities appear.
These authentication and access control mechanisms help Pasonet create a balanced approach. Users get strong security without sacrificing convenience—protecting customers and maintaining financial transaction system integrity.
Real-Time Threat Detection and Response Systems
Pasonet Technologies goes beyond encryption and authentication by setting up advanced monitoring systems to scan transactions for suspicious activities. The company identifies and stops threats before they affect users or put financial data at risk.
Anomaly Detection Using Machine Learning
The company employs advanced machine learning algorithms to analyze transaction patterns and spot unusual behavior. This AI-driven system breaks down massive amounts of data in real-time. Traditional security measures don’t deal very well with high transaction volumes, but this system offers faster and more accurate threat detection.
The anomaly detection system runs through several connected mechanisms:
- Behavioral analytics – Monitors user activities to identify suspicious patterns that might indicate fraudulent transactions
- Transaction pattern analysis – Flags unusual login attempts from unfamiliar locations or unexpected withdrawals
- System usage monitoring – Detects unauthorized access requests or abnormal transaction volumes
The security systems filter false positives through machine learning. This helps security teams focus where needed most. The platform screens for known fraud patterns and raises alerts about new suspicious activities through supervised and unsupervised learning.
Research shows AI-driven fraud detection systems can reduce financial fraud losses by up to 50%. Pas-net.com users benefit from quick action against threats. The system isolates compromised accounts, blocks malicious IP addresses, and flags suspicious transactions for manual review.
SIEM Integration for Log Analysis
Pasonet Technologies builds a resilient security system through Security Information and Event Management (SIEM) integration. The system combines security logs from multiple sources across the company’s infrastructure. This gives a central view of potential threats.
The SIEM integration follows several key steps:
The company first identifies data sources throughout its network. It collects security information from devices, servers, applications, and endpoint systems. Next, this data changes to a standard format for unified analysis. The SIEM software then relates events across different sources to spot patterns of potential security incidents.
The system creates alerts when it spots suspicious activity. These alerts notify the right personnel or trigger automated responses. All data gets stored to help with historical analysis, forensics, and compliance reporting.
SIEM integration gives Pasonet users major benefits:
- Real-time analysis – Immediate examination of security events as they occur
- Advanced correlation – Identification of complex attack patterns across different systems
- Proactive threat detection – Using behavioral analytics to identify risks before they escalate
Adding threat intelligence feeds to Pasonet’s SIEM helps relate security alerts better. This leads to more accurate threat detection and faster response times.
Incident Response Workflow in Pasonet Technologies
Pasonet Technologies starts a structured incident response workflow when it spots potential security incidents. The company follows a tested method based on real-life experience from thousands of incidents.
The incident response process has these key phases:
- Scope definition – Assessing the breadth, severity, and nature of the security incident
- Investigation – Using advanced tools for evidence collection and analysis to flag indicators of compromise
- Containment and eradication – Removing threats with custom eradication strategies while monitoring for new malicious activity
- Reporting and support – Providing detailed investigation reports and guidance for implementing additional security controls
This intelligence-driven approach helps pas-net.com maintain service even during active threats. The security team can start investigations quickly and gather evidence by using top-tier tools.
Automated responses trigger within milliseconds of detecting threats. This allows quick containment before threats grow. Pasonet’s incident response team works with one of the world’s largest cyberthreat research teams. Their threat hunters and malware reverse engineers stay proactive against new threats.
This detailed approach to threat detection and response helps Pasonet Technologies Private Limited keep its payment infrastructure strong against new cybersecurity challenges. Users can feel confident about their financial transactions’ security.
Security Audits and Penetration Testing Practices
Security assessments are the foundations of Pasonet’s protection strategy. These assessments help test if security measures work against real-life threats. Pasonet Technologies Private Limited uses structured testing programs to check if its defenses stay strong as threats keep changing.
Quarterly Penetration Testing by External Firms
Pasonet Technologies runs thorough penetration tests every three months. This goes beyond the yearly minimum that security standards recommend. The company tests this often because financial services face high risks. Even small security gaps can cause big money losses or data breaches. These tests copy real-life cyberattacks and check both network and application layers to find weak spots.
The company picks qualified testers with relevant certifications (CISSP, CEH, OSCP) carefully. These experts must know fintech payment systems well. Tests verify authentication flows, check API endpoints to stop injection attacks, and make sure data stays separate. They also confirm encryption works at every step—when data sits still, moves around, or gets processed.
Internal Vulnerability Scanning Tools
Pasonet runs internal vulnerability scans between outside assessments. Unlike regular external tests, these automatic tools work non-stop to spot problems before anyone can use them. The company uses two types of vulnerability scans:
- Internal scans that find weak spots insiders might use
- External scans that check risks from the internet
The company runs extra vulnerability scans right after security updates or big system changes. This quick check helps confirm that fixes work and don’t create new problems.
Bug Bounty Program for Ethical Hackers
Pasonet’s bug bounty program works with ethical hackers worldwide to boost security. Security researchers get rewards when they find and report problems before bad actors can use them.
Money rewards depend on how serious the problem is. The program focuses on authentication bypass issues, encryption problems, and unauthorized data access. Outside security experts bring fresh points of view. They help find tricky problems that normal testing might miss.
These ethical hackers know special tricks and look at things without bias. They often spot weak points that internal teams might not see. Pasonet uses regular penetration testing, non-stop internal scanning, and help from many security experts. This mix creates a framework that checks if security controls work well.
User-Facing Security Features on pas-net.com
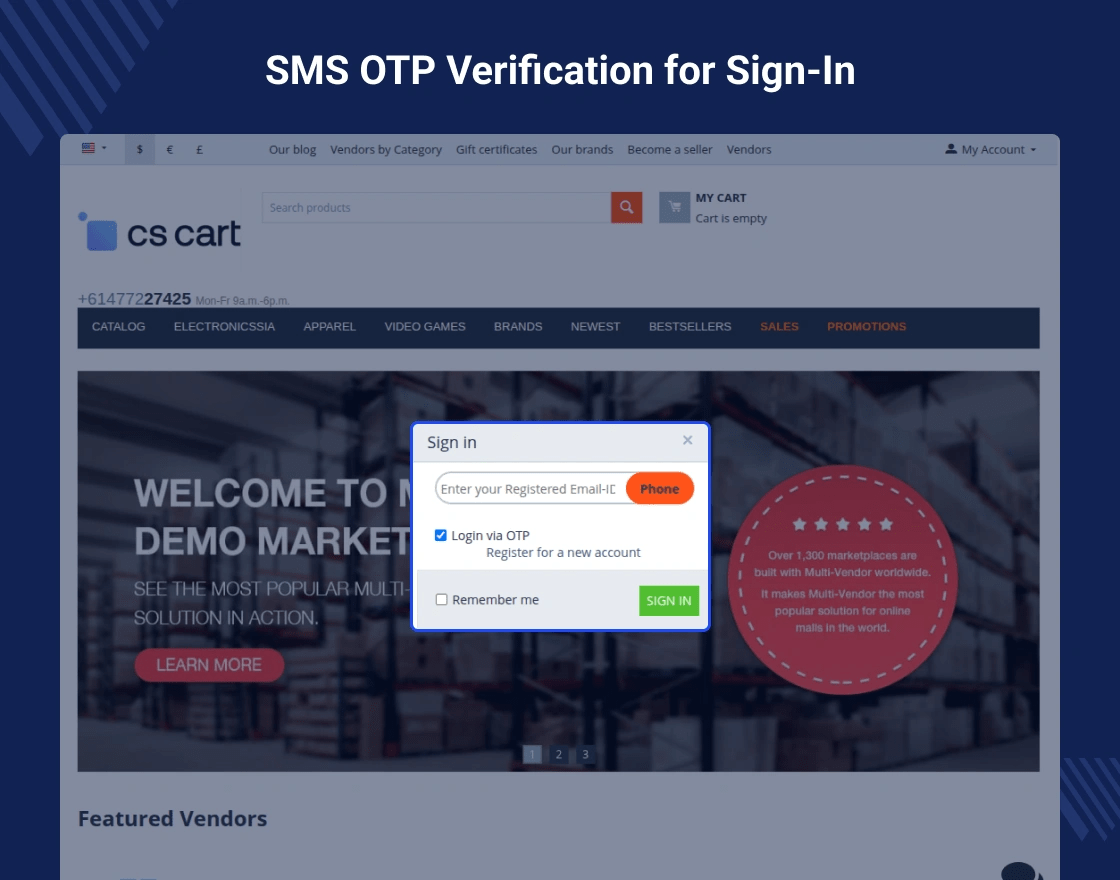
Image Source: Webkul Store
Pasonet focuses on backend security and gives users strong security features on pas-net.com. These client-side protections give users transparency and control over their account safety.
Login History and Device Management
Pasonet technologies gives users clear visibility into account access patterns. The platform records security events with IP addresses plus date and time stamps for all account activities. Users can see their currently logged-in devices in the security settings section to monitor active sessions. The platform shows geographic locations of login attempts based on IP lookup, though these locations show ISP registrations rather than actual device positions.
Transaction Verification via OTP
One-time passcodes (OTPs) are the life-blood of transaction security on pasonet technologies private limited. These unique, dynamic codes verify specific transactions and confirm user identity beyond standard credentials. We used these codes during online payments, fund transfers, or platform logins so only users with physical access to registered devices can authorize transactions. The system sends time-sensitive codes through SMS to registered mobile numbers, with email delivery as an alternative.
Secure Payment Gateway Interface Design
Pasonet’s payment interface uses visual security indicators that build user trust. SSL encryption verification shows through padlock icons and “https” in browser address bars. The interface displays trusted payment method logos with security assurance symbols to show that transactions happen in protected environments.
Conclusion
Pasonet Technologies protects digital transactions through its detailed security infrastructure. The company combines layered security, zero trust network architecture, and cloud-based redundancy to shield against cyber threats. On top of that, it uses advanced encryption standards like AES-256 for stored data and TLS 1.3 for information in transit to protect transactions at every stage.
Strong authentication mechanisms make this protection even more secure. The platform’s OAuth 2.0 integration, multi-factor authentication, and automatic session management strike the right balance between security and convenience. This balance matters more than ever as cybercriminals develop sophisticated attack methods.
Up-to-the-minute data analysis adds another vital defense layer to Pasonet’s ecosystem. Machine learning algorithms watch transaction patterns while SIEM integration examines security logs from multiple sources. The system triggers immediate response protocols when it detects suspicious activity, which helps maintain service integrity during threats.
The company’s defense strategy relies on regular security audits as its final verification layer. Quarterly penetration testing, vulnerability scanning, and an innovative bug bounty program keep security measures strong against new threats. These proactive checks spot potential weaknesses before attackers can exploit them.
User security features round out this detailed protection strategy. The platform enables users to monitor login history, verify transactions through OTPs, and access secure payment gateway interfaces. These tools give users transparency and control over their account safety.
Pasonet Technologies prioritizes security without sacrificing ease of use. The platform delivers both resilient protection and smooth user experience, making it perfect for businesses and individuals who need secure online transaction processing. This steadfast dedication to security will remain central to Pasonet’s value as digital payment systems continue their rise in the years ahead.
FAQs
1. How does Pasonet protect online transactions?
Pasonet uses advanced encryption techniques like AES-256 for stored data and TLS 1.3 for data in transit. It also employs a layered security model, zero trust network architecture, and real-time threat detection using machine learning algorithms to safeguard all transactions.
2. What authentication methods does Pasonet use?
Pasonet implements multi-factor authentication via SMS and email, OAuth 2.0 for third-party app integration, and session timeout features. These methods ensure that only authorized users can access accounts and perform transactions.
Q3. How often does Pasonet conduct security audits?
Pasonet conducts quarterly penetration testing by external firms, surpassing the industry standard of annual testing. Additionally, it uses continuous internal vulnerability scanning tools and operates a bug bounty program for ethical hackers to identify potential security weaknesses.
4. What user-facing security features does Pasonet offer?
Pasonet provides users with login history and device management capabilities, transaction verification via one-time passcodes (OTPs), and a secure payment gateway interface. These features give users transparency and control over their account security.
5. How does Pasonet handle potential security threats?
Pasonet employs real-time threat detection systems using machine learning for anomaly detection. It also integrates Security Information and Event Management (SIEM) for comprehensive log analysis. When a potential threat is detected, Pasonet activates a structured incident response workflow to contain, investigate, and resolve the issue efficiently.

